Share this
Security Rights Management for Lease Administration
by Dan Galenkamp on May 17, 2017
The ability to manage lease data securely is of the utmost importance for real estate teams.
For lease administration software, the ability to manage data securely is of the utmost importance. With the responsibility of not only managing the data, but also controlling the other end users, the administrator plays a crucial role in maintaining the security of the system. When looking for a software that is going to maximize efficiency while minimizing liabilities, one must make sure that the software is capable of managing users, maintaining data records, maintaining security groups, and running security rights reports.
As the administrator for a software that handles a high volume of critical data, the software needs to be able to easily control user’s access. With CoStar’s proprietary software not only can administrators disable and delete accounts quickly and easily for employees leaving the company, they can also add an unlimited number of user accounts to access the database. CoStar’s method of pricing based on number of leases instead of number of users gives administrators more freedom to let the information be accessible through multiple departments while still maintaining tight control of who can see it.
Another function that is important when choosing a software system is the system needs to have objects that are easy to find and control. In CoStar’s software any record can be searched by its ID, by name, through key terms, or even through filtering the database by various criteria. Once the record of data is created, CoStar’s software gives administrators the ability to see what users and groups have rights to the information and quickly change the security settings for any object. This gives the ability to have multiple levels of access for different information, which is important in keeping information secure.
Continuing on the topic of varied levels of access, CoStar’s software gives administrators the ability to change access levels for large groups quickly through the use of security groups. Instead of having to go through and change the security access for each user like in some software, administrators can quickly make changes to access levels of security groups and then add or remove individual users from the groups. These security groups add another level of convenience and functionality to help increase security while increasing efficiency at the same time.
The last security function that administrators need to look for when choosing a software is the ability to run different security reports. With CoStar’s software there are a number of security reports that can be easily run including a group and user history report, a group and user module rights report, and a group and user navigation rights report. All of these reports give different insights on the behaviors of the user and the security of the information in a way that is convenient for the administrators to use.
In conclusion, when choosing a software, the lease administrators need to find a software that has the functionality to maximize security while streamlining processes. Any potential software needs the ability to easily control users, objects, and groups in a way that increases regulation while saving time. The software also needs to be able to run comprehensive security reports to be able to protect the information. CoStar’s proven track record and ability to perform these crucial functions makes it the optimal choice for companies who value security.
Share this
- ASC 842 (78)
- Lease Accounting Software (59)
- Accounting Teams (36)
- Lease Administration Software (13)
- Retail Tenants (12)
- Commercial Real Estate (8)
- Lease Management (8)
- Market Data and Analytics (7)
- Real Estate Teams (5)
- Success Stories (5)
- News and Media Coverage (2)
- Transaction Management Software (2)
- Customer Success (1)
- Office Tenants (1)
- April 2024 (1)
- February 2024 (1)
- December 2023 (4)
- November 2023 (6)
- October 2023 (4)
- September 2023 (2)
- August 2023 (2)
- July 2023 (3)
- May 2023 (2)
- March 2023 (1)
- February 2023 (3)
- December 2022 (3)
- November 2022 (4)
- October 2022 (4)
- September 2022 (1)
- August 2022 (4)
- June 2022 (1)
- May 2022 (4)
- April 2022 (8)
- March 2022 (3)
- February 2022 (1)
- October 2021 (2)
- September 2021 (1)
- August 2021 (15)
- July 2021 (3)
- June 2021 (1)
- May 2021 (1)
- April 2021 (3)
- March 2021 (1)
- January 2021 (1)
- December 2020 (3)
- November 2020 (1)
- October 2020 (2)
- September 2020 (2)
- August 2020 (3)
- July 2020 (2)
- June 2020 (3)
- May 2020 (1)
- April 2020 (1)
- March 2020 (1)
- February 2020 (1)
- December 2019 (1)
- October 2019 (1)
- September 2019 (2)
- August 2019 (3)
- July 2019 (2)
- April 2019 (69)
- October 2018 (1)
- August 2018 (1)
- July 2018 (1)
- June 2018 (1)
- May 2018 (1)
- April 2018 (2)
- March 2018 (3)
- February 2018 (2)
- December 2017 (1)
- August 2017 (3)
- June 2017 (2)
- May 2017 (2)
- April 2017 (1)
- March 2017 (2)
- January 2017 (2)
- November 2016 (2)
- July 2016 (1)
- June 2016 (1)
- July 2015 (1)
- March 2015 (1)
- June 2014 (1)
- April 2014 (11)
- October 2011 (1)
You May Also Like
These Related Stories

Lease Accounting Compliance – 3 Critical Steps for Success
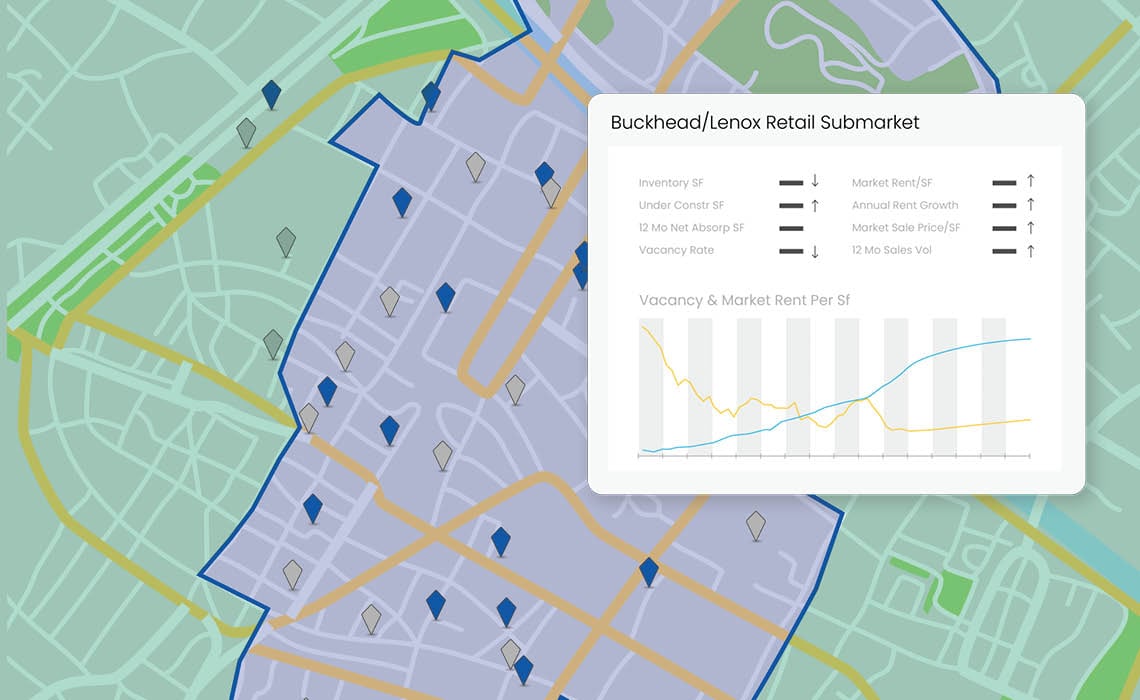
Why lease administrators need integrated market data